Find who is stealing your Wi-Fi and what you can do to block them
Table of Contents
Someone steals your wifi ? learn how to block their connection
Identify if a neighbor steals wifi and block their connection so they can’t connect anymore is very easy and simple with the following steps described below.
Here are some simple ways to find out
who is stealing your Wi-Fi and what you can do to block them and protect your network.
It is increasingly common for people to run out of data on their cell phones and make use of neighboring Wi-Fi networks, making use of an unauthorized connection and in some cases causing the owner a slow or problematic Internet connection.
Nowadays, every internet line, ADSL, fibre optic connection, etc comes installed with a Wi-Fi router. This means that each building has a large number of wireless networks available. For this reason, many people consider not hiring their own Internet line and use their neighbor’s.
Different methods are used to illegally use a Wi-Fi network:
- Weak or predictable passwords.
- Wi-Fi password cracking, either by the use of old fashioned security mechanisms or because the password appears in a dictionary.
- Default Wi-Fi password created based on patterns.
This last point is very common since routers usually come with a generic or pre-generated Wi-Fi network name and a password calculated based on patterns. Many of these patterns have been discovered so that passwords can be easily calculated and figured out regardless of whether the Wi-Fi security is set to maximum security.
At home, neighbors who usually don’t want to pay for an internet connection, may connect to your Wi-Fi network. In places such as bars, restaurants, hotels, which provide free Wi-Fi for their customers, neighbors or even tourists use their Wi-Fi since there are many pages and apps that collect passwords around the world.
If someone uses your Wi-Fi network and this person is engaged in criminal acts, your Internet address (IP) will appear. This may cause you problems and although you haven’t committed any crime, it’s always better not to find yourself in that situation and take the necessary precautions.
How to detect if someone steals your wifi
How do we know if someone is using our Wi-Fi network without permission? There are 3 very simple and effective ways to find out.
1 – Taking a look at the router
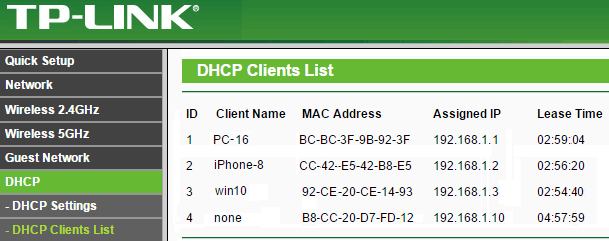
The router or access point has a list of the devices that are connected at all times.
By accessing the router or access point you may search the list of devices and check them one by one.
- PROS: The router gives us the information.
- CONS: You will have to access the router each time. If you have several SSIDs, one for 2.4 and another for 5GHz, you will have to look one by one. Some ISPs do not provide the router access credentials, or the option is simply not available.
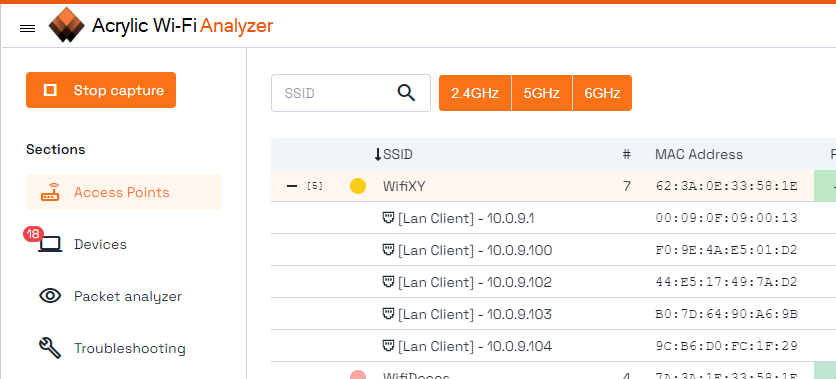
2 – Searching for devices connected to the Wi-Fi network
When a device connects to a network, whether Wi-Fi or wired, it obtains an IP address on the local network and is usually visible by other devices to share documents, etc.
Once connected to the network, we can scan and look for connected devices.
If we have an iPhone and an MSI as a laptop but we see that a Xiaomi is connected, we can be sure that that person steals wifi and we need to block its connection.
- PROS: Very simple and usually provides good results
- CONS: Sometimes networks isolate users and it’s impossible to detect them.
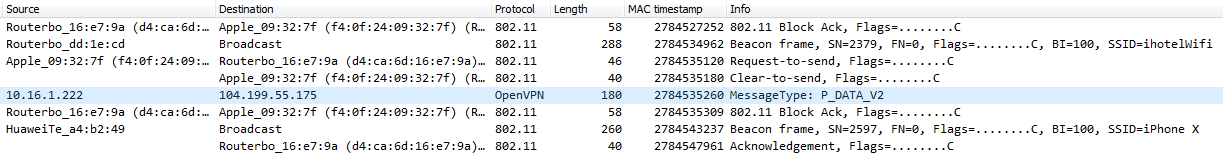
3 – Analysing Wireless Traffic
By using a card in monitor mode, with a wifi sniffer, you may view the Wi-Fi packets that are sent between clients and routers.
A cell phone sends and receives packets from a router in order to communicate. These data packets have a MAC address readable by anyone who is listening. This will enable you to detect which devices are talking to each other. You may find out which clients are connected to a Wi-Fi network, without having to be connected to it.
This is the best method since we don’t need to be connected to the network to find out if there’s people connected to it. In addition, it will always work with any router or access point regardless of its settings and features
- PROS: It always works, it is independent of the network settings and it doesn’t have to be connected to the Wi-Fi network.
- CONS: A card that supports monitor mode is required.
How to block who steals your wifi
Inventories will help us identify our devices quickly as well as those that don’t belong to us. Like this, we’ll be able to detect them and block them in a simple way.
1 – Changing password
It is the first basic and simple step that should be done when you suspect that someone is stealing your Wi-Fi connection.
If the network password is changed, the person using your Wi-Fi network will need to know the new password in order to connect again.
This has to be combined with a strong password and make sure the encryption isn’t WEP.
Since old passwords may be cracked by attackers, you should change your passwords periodically.
- PROS: Often the simplest and most effective option.
- CONS: Your device passwords should be changed but this isn’t always possible or simple.
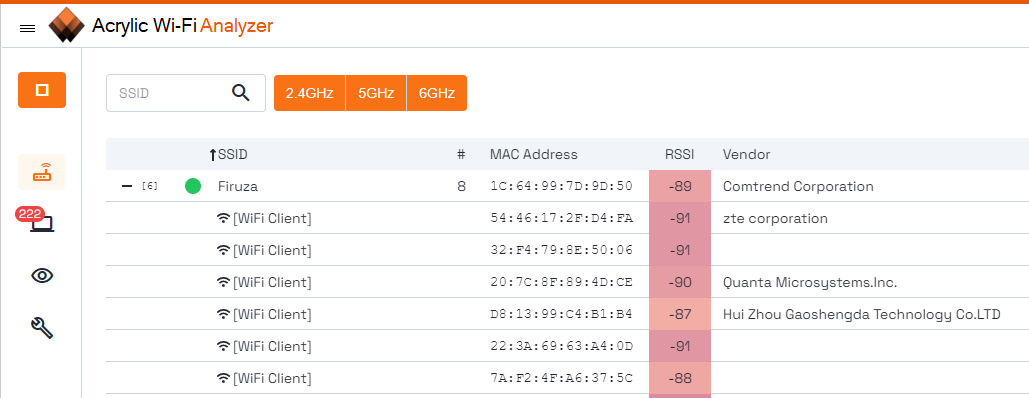
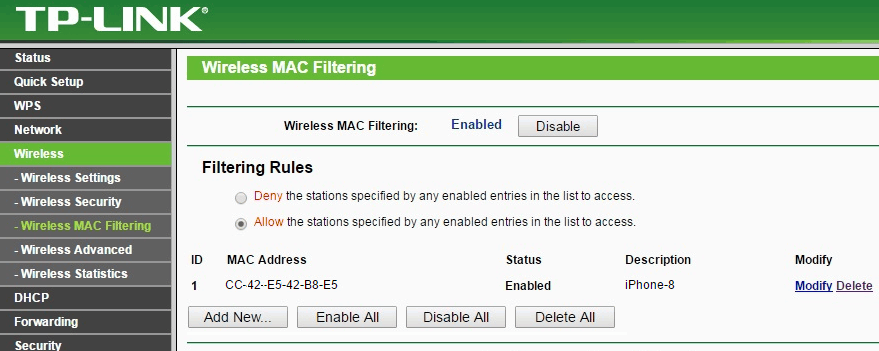
2 – Filtered by mac
If you know the MAC address, you may be able to block that particular device by filtering by mac. This option may work if you’re not a very experienced user. However, it would be enough for the intruder to change its MAC address to skip this filter, something that is quite easy to do on a computer.
- PROS:: It is supported by practically all current routers and is very easy to apply.
- CONS: An attacker will be able to obtain valid MAC addresses or change his/her own to skip the MAC address white/blacklists and log on to the network.
Conclusions on how to find out who steals your wifi and block their connection
Finally, please remember that hiding the SSID is not a security or protection mechanism. Finding out the hidden name of a Wi-Fi network is very easy to do and does not offer any kind of security against attackers.
If your internet connection is slow or the line fails, you must find out if someone is stealing your Wi-Fi connection. If that is the case, the necessary actions will be taken to try to stop it by blocking it and changing the access passwords.
Finally, if your connection still doesn’t work properly, an analysis should be made of the status and functioning of it, the channel, bandwidth, coverage, etc. Like this, you’ll be able to measure what isn’t working properly and get recommendations on how to improve your Wi-Fi.
Discover your Wi-Fi thief and block them using Acrylic Wi-Fi Analyzer
This article is part of a series of articles about WiFi setup for teleworking and small offices
- How to improve WiFi Performance and Coverage
- WiFi Device & AP Inventory
- Is a Hidden WiFi Network Secure? (Hidden SSID)
- Find who is stealing your Wi-Fi and what you can do to block them
- Teleworking wifi, how to get the best performance
- 6 steps to create a secure wifi network at home